Automating Identity Lifecycle in SUSE Rancher Prime with SCIM
 As Kubernetes footprints grow, keeping user identities in sync gets harder. SUSE Rancher Prime already helps here. Automatic identity refresh keeps user and group data up to date for providers that support querying, and the user retention process cleans up inactive accounts over time. But gaps remain: not all providers can be queried for changes, user provisioning still requires a first login, and retention policies can only react after the fact. What is missing is a way for the IdP to push identity changes as they happen.
As Kubernetes footprints grow, keeping user identities in sync gets harder. SUSE Rancher Prime already helps here. Automatic identity refresh keeps user and group data up to date for providers that support querying, and the user retention process cleans up inactive accounts over time. But gaps remain: not all providers can be queried for changes, user provisioning still requires a first login, and retention policies can only react after the fact. What is missing is a way for the IdP to push identity changes as they happen.
SUSE Rancher Prime v2.14 introduces experimental support for SCIM (System for Cross-domain Identity Management) identity provisioning. SCIM lets your Identity Provider push user and group changes to Rancher automatically, so accounts stay current without manual work and help meet compliance requirements. It is available exclusively to SUSE Rancher Prime customers.
The Challenge: Identity Sync Gaps in Kubernetes Platforms
Today, SUSE Rancher Prime provisions user accounts when they first log in or when administrators manually add them as project or cluster members. This works, but it means Rancher’s user data is only as current as the last login or manual update.
There are still a few areas where things could be smoother:
– Delayed onboarding: Users can be added as cluster or project members before they log in, but this requires knowing and manually adding each user upfront. Ideally, accounts would be provisioned automatically from the IdP — no manual steps needed.
– Keeping identity data current: When an employee leaves, changes roles, or moves teams, Rancher’s user and group data may not reflect reality right away. Account deactivation depends on manual action or a retention policy catching up, and for SAML and OIDC providers, group memberships only refresh at login time. The existing automatic refresh and retention features help, but there is still a window where data can drift.
These gaps widen with scale. The more users and clusters you manage, the harder it is to keep identity data consistent.
The Solution: SCIM Identity Provisioning
OIDC and SAML verify who a user is. SCIM is different: it manages the full identity lifecycle. Accounts are created before first login, profile and group changes sync in real time, and users are deactivated the moment they are disabled in the IdP.
With SCIM in Rancher Prime, your IdP pushes identity changes to Rancher as they happen. No polling, no manual intervention.
How It Works
SCIM 2.0 is an IETF standard (RFC 7643, RFC 7644) built for automated identity provisioning. When SCIM is enabled, Rancher Prime is a SCIM Service Provider: it exposes a standards-compliant REST API that your IdP calls directly. In practice:
– Users join the organization. The IdP automatically provisions their account in Rancher. Administrators can pre-assign roles and permissions before the user ever logs in.
– Users change teams or roles. Group memberships update in Rancher immediately, so permissions match the actual org structure.
– Users leave or are disabled. Their Rancher account is deactivated and active sessions are terminated.
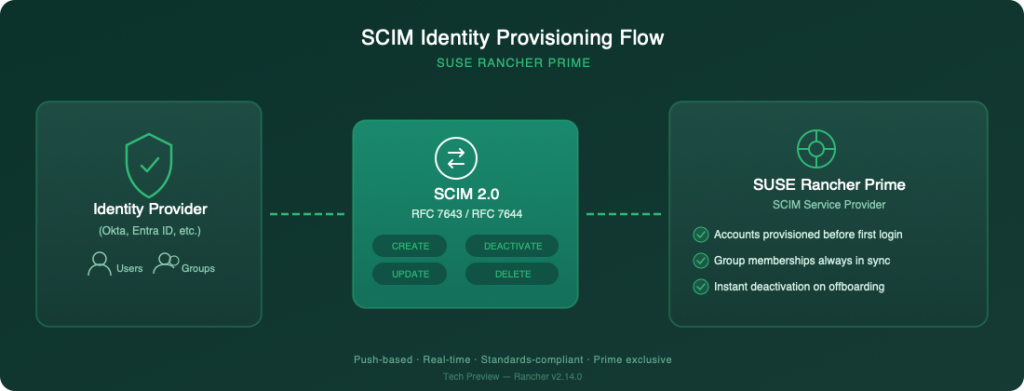
SUSE Rancher Prime SCIM Identity Provisioning
Key Capabilities
– Automated user provisioning and deprovisioning: Users and groups are created, updated, and deactivated in Rancher automatically based on IdP changes.
– Real-time synchronization: Changes propagate immediately, without sync windows or polling delays.
– Group lifecycle management: IdP groups are provisioned into Rancher, and membership stays in sync as users are added or removed.
– Per-provider configuration: SCIM can be enabled independently for each authentication provider, so administrators control it per provider.
– Secure token-based authentication: Communication between the IdP and Rancher is secured using bearer tokens with constant-time validation.
A Prime Capability for Enterprise Identity Governance
SCIM identity provisioning is available exclusively to SUSE Rancher Prime customers. Because your IdP owns the identity lifecycle, SCIM in Rancher Prime helps you:
– Strengthen the security posture: Orphaned accounts and stale access go away because deprovisioning happens automatically.
– Simplify audits: Automated identity management helps satisfy SOC 2, ISO 27001, NIST, and GDPR requirements for timely, accurate account lifecycle tracking.
– Save time: Platform engineers stop spending time on manual user and group management.
– Scale confidently: SCIM keeps identities consistent whether you have fifty users or five thousand.
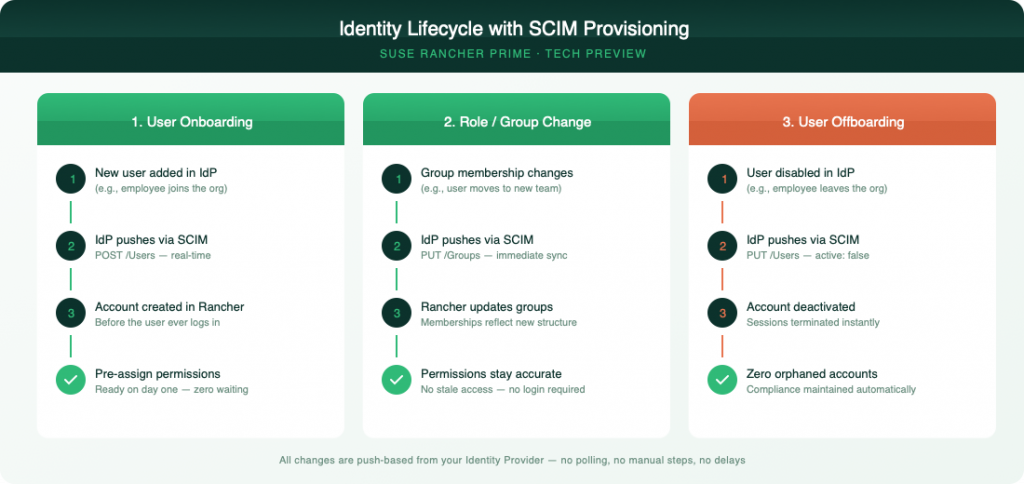
SUSE Rancher Prime SCIM Identity Lifecycle
Getting Started
SCIM identity provisioning ships as a Tech Preview in SUSE Rancher Prime v2.14.0 with integration support for Okta. Support for Microsoft Entra ID is planned for the SCIM general availability release.
Since SCIM is an open standard supported by major identity providers including Okta, Azure AD (Entra ID), OneLogin, Google Workspace, and PingIdentity, you can expect broad compatibility as the feature matures.
To get started, enable the SCIM feature flag and configure a bearer token for IdP-to-Rancher communication. The setup fits into Rancher’s existing authentication provider configuration, and the API-driven approach works well with infrastructure-as-code workflows. For detailed instructions, see the SCIM identity provisioning documentation.
We encourage SUSE Rancher Prime early adopters to try SCIM provisioning in non-production environments and share feedback to help shape the feature as it progresses toward general availability.
Automating Identity Governance: The Power of SCIM in Rancher Prime
SCIM provisioning means user accounts and group memberships in Rancher stay in sync with your IdP, without manual work. Accounts are created before first login, updated when roles change, and deactivated when people leave.
Your IdP already owns identity data. With SCIM, Rancher Prime keeps it that way.
Come see us at KubeCon EU in Amsterdam. Visit the SUSE booth, join our sessions, and experience firsthand what an AI-native cloud native platform can do for your organization.
For the latest updates, visit suse.com/kubecon and follow us on social media throughout the week.
Blog authored by Peter Matseykanets, Principal Software Engineer, SUSE

Related Articles
Jan 17th, 2025